Paragon Graphite Spyware used a zero-day exploit to hack at least two journalists’ iPhones

Security researchers at Citizen Lab revealed that Paragon’s Graphite spyware can hack fully updated iPhones via zero-click attacks.
Citizen Lab has confirmed that Paragon’s Graphite spyware was used to hack fully updated iPhones, targeting at least two journalists in Europe. The group found forensic evidence showing the phones had communicated with the same spyware server. Apple quietly alerted the victims earlier this year, marking the first confirmed case of Paragon’s tools being used in real-world attacks.
On April 29, 2025, Apple alerted select iOS users of spyware targeting. Forensic analysis confirmed that two journalists, including Ciro Pellegrino, were infected with Paragon’s Graphite spyware. Both cases were linked to the same attacker. Apple has since patched the zero-click exploit used in the attack, now tracked the flaw as CVE-2025-43200, in iOS version 18.3.1.
In April 2025, a European journalist who has requested to remain anonymous received an Apple alert and requested technical help. Forensics analysis of its device revealed it was infected with Paragon’s Graphite spyware via a zero-click iMessage attack in Jan–Feb 2025, while running iOS 18.2.1.
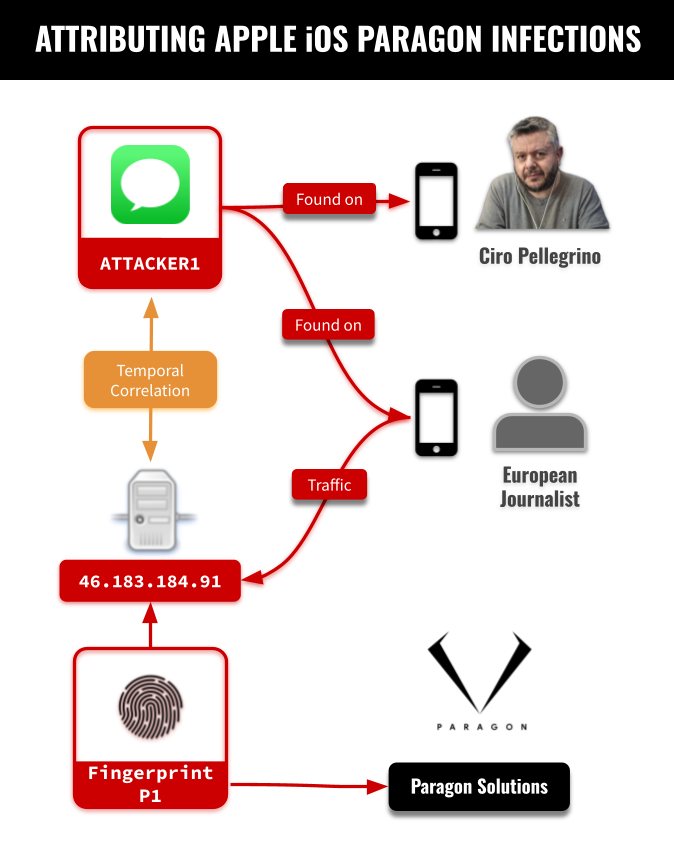
“Our forensic analysis concluded that one of the journalist’s devices was compromised with Paragon’s Graphite spyware in January and early February 2025 while running iOS 18.2.1.” reads the report published by Citizen Labs. “We attribute the compromise to Graphite with high confidence because logs on the device indicated that it made a series of requests to a server that, during the same time period, matched our published Fingerprint P1.”
The researchers found in the logs evidence of connections to a known Paragon server, matched by fingerprint. Apple has since patched the exploited vulnerability (CVE-2025-43200) in iOS 18.3.1.

The Italian journalist Ciro Pellegrino was notified by Apple on April 29, 2025, of a spyware attack. Forensic analysis confirmed that also his iPhone was targeted with Paragon’s Graphite spyware. Logs showed the same ATTACKER1 iMessage account used in a previous case, linking both attacks to a single Graphite operator. The findings suggest a coordinated effort by one spyware customer. Investigations into Paragon’s tools and operations are still underway.

Ciro Pellegrino works for the Italian newsroom Fanpage.it, and also his colleague Francesco Cancellato, was notified in January 2025 by WhatsApp that he was targeted with Paragon’s Graphite spyware.
Citizen Lab’s analysis of Mr. Cancellato’s Android device found no forensic proof of infection, but due to Android’s limited logging, a hack can’t be ruled out. However, the fact that two journalists from the same newsroom were targeted with Paragon spyware raises concerns of a broader attempt to infiltrate the media outlet.
On June 5, 2025, Italy’s intelligence oversight committee (COPASIR) confirmed the government used Paragon’s Graphite spyware to spy on Luca Casarini and Dr. Beppe Caccia, but couldn’t determine who targeted journalist Mr. Cancellato. Paragon later claimed it offered help investigating, which Italy rejected over national security concerns. Italy also disputed Paragon’s claim of ending the contract. Paragon has not responded to Citizen Lab’s latest findings.
“In response later that day, the Italian Department of Security Intelligence (DIS: Dipartimento delle Informazioni per la Sicurezza), which coordinates Italy’s intelligence services, stated that it had rejected Paragon’s offer because of national security concerns with exposing their activities to Paragon. They stated that providing Paragon such access would impact the reputation of Italy’s security services among peer services around the world. They denied that the contract termination was unilateral.” concludes CitizenLab. “Later the same day, the COPASIR committee denied knowledge of Paragon’s offer of assistance and stated a willingness to declassify Paragon’s testimony to the committee.”
Early this week, Paragon accused the Italian government of refusing its offer to help investigate spyware use against a journalist. The company said this led to its decision to end contracts in Italy. Paragon claimed it proposed a way to verify if its tools were misused, but authorities declined. This marks the first time a spyware firm publicly cut ties with a client over alleged abuse. Paragon confirmed the statement’s accuracy but declined further comment.
“The company offered both the Italian government and parliament a way to determine whether its system had been used against the journalist in violation of Italian law and the contractual terms,” read Paragon’s statement published by TechCrunch. “As the Italian authorities chose not to proceed with this solution, Paragon terminated its contracts in Italy.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Paragon)