Experts warn of mass exploitation of critical PHP flaw CVE-2024-4577

Threat actors exploit PHP flaw CVE-2024-4577 for remote code execution. Over 1,000 attacks detected globally.
GreyNoise researchers warn of a large-scale exploitation of a critical vulnerability, tracked as CVE-2024-4577 (CVSS 9.8), in PHP. An attacker could exploit the vulnerability to achieve remote code execution on vulnerable servers using Apache and PHP-CGI.
The flaw CVE-2024-4577 (CVSS score: 9.8) is a PHP-CGI OS Command Injection Vulnerability. The issue resides in the Best-Fit feature of encoding conversion within the Windows operating system. An attacker can exploit the flaw to bypass protections for a previous vulnerability, CVE-2012-1823, using specific character sequences. Consequently, arbitrary code can be executed on remote PHP servers through an argument injection attack, allowing attackers to take control of vulnerable servers.
Since the disclosure of the vulnerability and public availability of a PoC exploit code, multiple actors are attempting to exploit it, reported Shadowserver and GreyNoise researchers.
In June, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the the vulnerability to its Known Exploited Vulnerabilities (KEV) catalog.
In July 2024, the Akamai Security Intelligence Response Team (SIRT) warned that multiple threat actors were exploiting the PHP vulnerability CVE-2024-4577 to deliver multiple malware families, including Gh0st RAT, RedTail cryptominers, and XMRig.
“Threat actors continued the speedy-time-from-disclosure-to-exploitation trend and were quick to leverage this new vulnerability — we observed exploit attempts targeting this PHP flaw on our honeypot network within 24 hours of its disclosure.” reported Akamai.
At the time, Greynoise researchers also reported malicious attempts of exploitation of the CVE-2024-4577.
“As of this writing, it has been verified that when the Windows is running in the following locales, an unauthorized attacker can directly execute arbitrary code on the remote server:
- Traditional Chinese (Code Page 950)
- Simplified Chinese (Code Page 936)
- Japanese (Code Page 932)
For Windows running in other locales such as English, Korean, and Western European, due to the wide range of PHP usage scenarios, it is currently not possible to completely enumerate and eliminate all potential exploitation scenarios.” continues the advisory. “Therefore, it is recommended that users conduct a comprehensive asset assessment, verify their usage scenarios, and update PHP to the latest version to ensure security.
Akamai researchers also observed threat actors behind the DDoS botnet Muhstik exploiting this vulnerability.
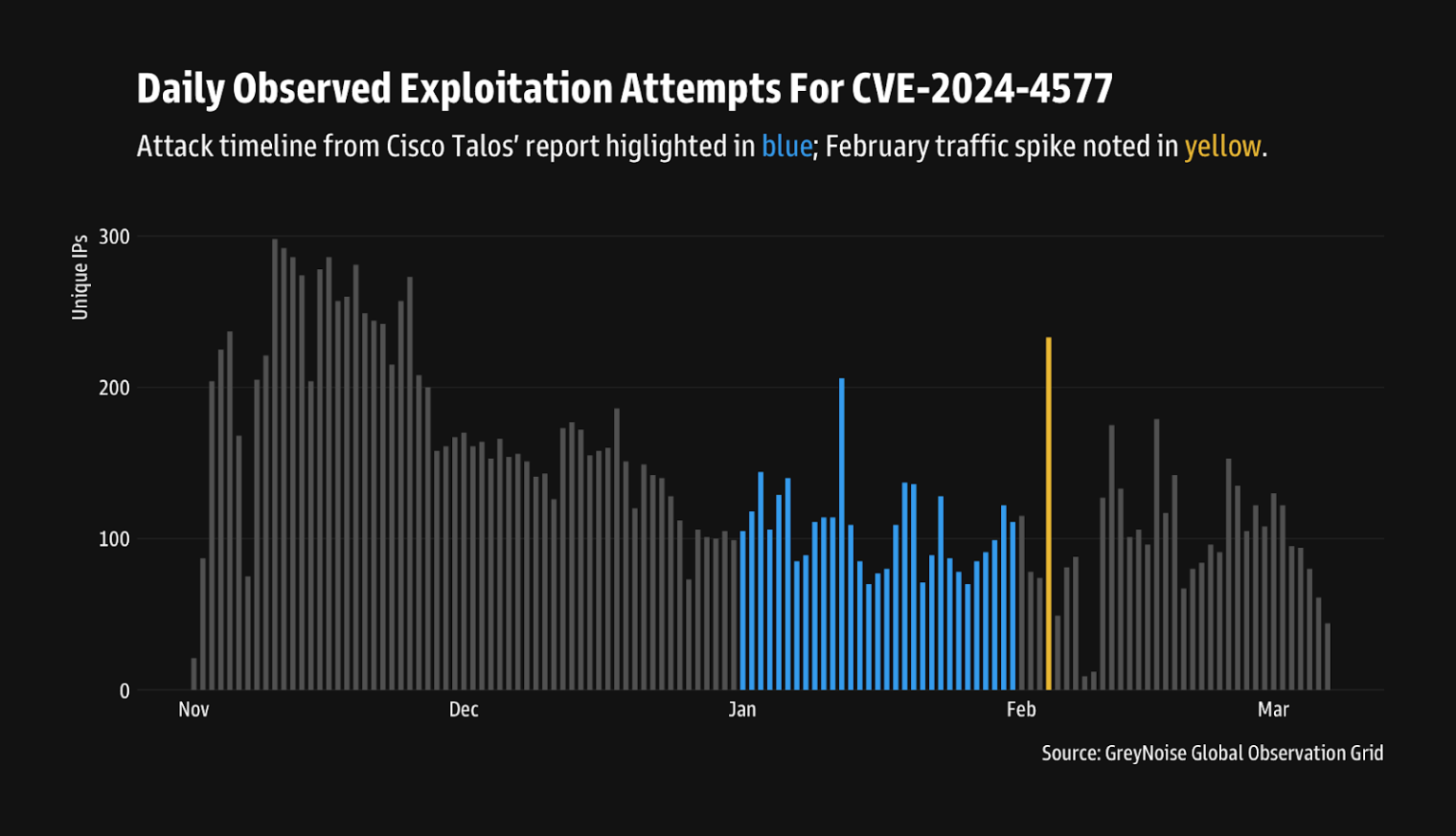
Last week, Cisco Talos researchers reported that an unknown threat actor has been exploiting the flaw since as early as January 2025, predominantly targeting organizations in Japan.
Now, GreyNoise researches confirm the large scale exploitation of CVE-2024-4577 and warns that it is not limited to Japanese entities. The experts observed a surge in the attacks against the US, the UK, Singapore, Indonesia, Taiwan, Hong Kong, India, and Spain.
“GreyNoise data confirms that exploitation of CVE-2024-4577 extends far beyond initial reports. Attack attempts have been observed across multiple regions, with notable spikes in the United States, Singapore, Japan, and other countries throughout January 2025.” reads the advisory.
GreyNoise detected 1,089 unique IPs exploiting CVE-2024-4577 in January 2025, with attacks spreading beyond Japan to Singapore, Indonesia, the UK, Spain, and India. Over 43% of attacks originate from Germany and China. In February, a coordinated spike in global exploitation suggested increased automated scanning for vulnerable systems.


The company urges users to update their installations as soon as possible.
“Organizations with internet-facing Windows systems exposing PHP-CGI — especially those in these newly identified targeted regions — should follow the guidance provided by Cisco Talos and perform retro-hunts to identify similar exploitation patterns.” concludes GreyNoise.
“Identify and block malicious IPs actively targeting CVE-2024-4577. “
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, PHP-CGI OS Command Injection Vulnerability)