Cryptojacking campaign relies on DevOps tools

A cryptojacking campaign is targeting exposed DevOps servers like Docker and Gitea to secretly mine cryptocurrency.
Wiz researchers uncovered a cryptojacking campaign, tracked as JINX-0132, targeting exposed DevOps applications like Nomad, Consul, Docker, Gitea to secretly mine cryptocurrency.
Threat actors behind the campaign are exploiting a wide range of known misconfigurations and vulnerabilities to deliver the miner.
This campaign is the first publicly known case of attackers exploiting misconfigured Nomad servers in real-world attacks. The group behind it, named JINX-0132, took advantage of this overlooked entry point, much like in a previous campaign, “SeleniumGreed,” which targeted exposed SeleniumGrid setups. These types of misconfigurations often go unnoticed by defenders, especially when the tools involved aren’t widely seen as likely attack targets.
The threat actor behind this cryptojacking campaign rely on public GitHub tools and standard XMRig versions instead of custom malware. This “living-off-open-source” approach complicates attribution and clustering. Some compromised Nomad servers control hundreds of clients, showing that even large, resource-rich organizations can fall victim to simple misconfigurations.
“A key characteristic of JINX-0132’s methodology is the seemingly deliberate avoidance of any unique, traditional identifiers that could be used by defenders as Indicators of Compromise (IOCs). Instead of utilizing attacker-controlled servers for payload delivery, they download tools directly from public GitHub repositories.” reads the report published by cloud security firm Wiz. “Furthermore, they rely on standard release versions of XMRig rather than custom malware.”
The campaign targets misconfigured Nomad servers that are publicly exposed and running with default settings. By abusing Nomad’s job queue feature, which are enabled by default unless reconfigured, attackers like JINX-0132 can remotely submit jobs without authentication. They use this access to run shell commands that download and execute the XMRig crypto miner from GitHub, using an attacker-controlled Monero wallet. Since this attack doesn’t rely on custom malware or attacker-owned infrastructure, it’s harder to detect, with the only clear indicator being the wallet address, easily changed for future attacks. This highlights the importance of properly securing Nomad’s API access and following HashiCorp’s recommended configurations.
JINX-0132 targets publicly exposed Gitea servers by exploiting misconfigurations or known vulnerabilities. While the exact method varies, possible attack paths include:
- Post-authentication RCE (CVE-2020-14144) in versions 1.1.0–1.12.5 if git hooks are enabled and attackers gain user access.
- Unauthenticated RCE in version 1.4.0 via a logic flaw that allows forging admin sessions and executing malicious hooks.
- Unlocked installer, allowing attackers to rerun setup and reset admin credentials.
These weaknesses allow attackers to gain code execution and establish a foothold on vulnerable servers.
Threat actors target misconfigured Consul servers by abusing the service registration and health check features. Without proper security settings like ACLs, any remote user can register services and execute health checks—bash commands run on connected nodes. JINX-0132 used this to run XMRig miners under random service names, exploiting default settings for remote code execution and cryptomining.
Attackers can exploit misconfigured Docker servers by abusing the exposed Docker Engine API, which allows full control over containers. If admins expose this API over the internet (e.g., via tcp://0.0.0.0:2375) threat actors can use it to run malicious containers, mount the host filesystem, or launch cryptominers. This gives them root-level access with just a few API calls, making remote code execution easy and dangerous.
“Based on Wiz data, 25% of all cloud environments have at least one of the above-mentioned technologies, with HashiCorp Consul being the most popular, running in over 20% of environments. Of those environments using these DevOps tools, 5% expose them directly to the Internet, and among those exposed deployments, 30% are misconfigured.” states Wiz.
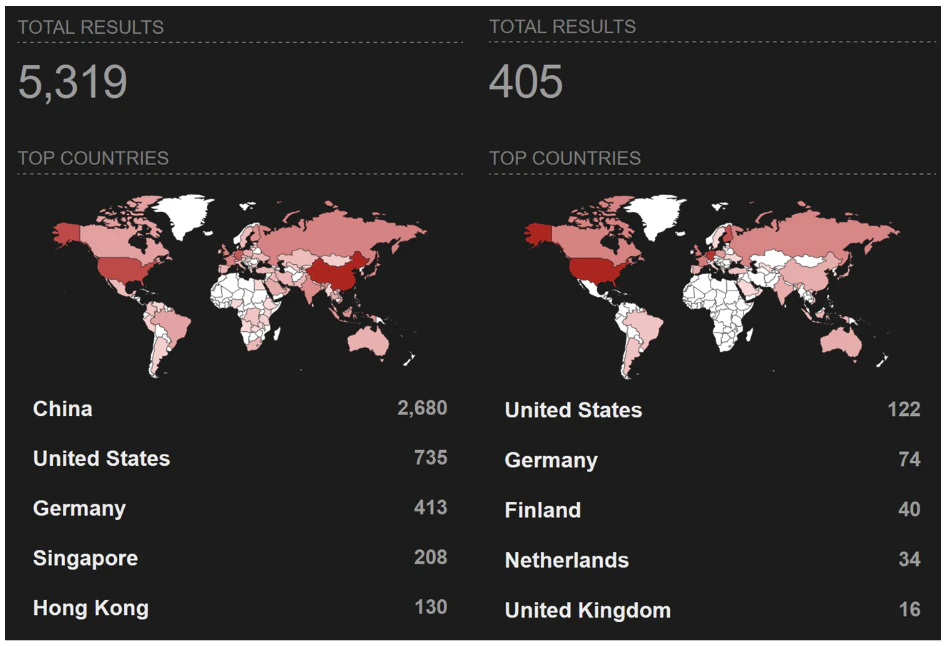
A Shodan search reveals thousands of exposed Consul and Nomad instances online, including hundreds hosted on major cloud platforms like AWS, Azure, and GCP. Most of the exposed servers are in China, the United States, Germany, Singapore, Hong Kong, Finland, the Netherlands, and the United Kingdom.

Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, cryptojacking campaign)