China-linked APT41 used Google Calendar as C2 to control its TOUGHPROGRESS malware

Google says China-linked group APT41 controlled malware via Google Calendar to target governments through a hacked site.
Google warns that China-linked APT41 used TOUGHPROGRESS malware with Google Calendar as C2, targeting various government entities via a compromised website.
” In late October 2024, GTIG discovered an exploited government website hosting malware being used to target multiple other government entities. The exploited site delivered a malware payload, which we have dubbed “TOUGHPROGRESS”, that took advantage of Google Calendar for command and control (C2).” reads the report published by Google. “Misuse of cloud services for C2 is a technique that many threat actors leverage in order to blend in with legitimate activity.”
APT41 used spear phishing emails with a ZIP file hosted on a hacked government site. The ZIP pretended to be a document about export declarations and included a disguised LNK file and images of arthropods. Two of the images were fake, one of them contained an encrypted payload, the other a DLL used to decrypt and launch the malicious code when the victim clicked the link. A decoy PDF was shown to avoid suspicion.
The malware operates in three stealthy stages, each with a specific role and advanced evasion tactics. The first stage PLUSDROP decrypts and runs the next stage entirely in memory. Then, the second stage PLUSINJECT uses process hollowing to inject malicious code into a legitimate Windows process like svchost.exe. Finally, TOUGHPROGRESS carries out the attacker’s tasks on the infected system, communicating with its operators through Google Calendar to avoid detection.
TOUGHPROGRESS starts by decrypting embedded shellcode using a hardcoded XOR key, then decompresses a DLL in memory with LZNT1. This DLL uses advanced control flow obfuscation techniques, like register-based indirect calls, dynamic address arithmetic, 64-bit register overflow, and function dispatch tables, to hide its behavior. These tricks make it hard for analysis tools to trace how the malware operates, significantly complicating reverse engineering.
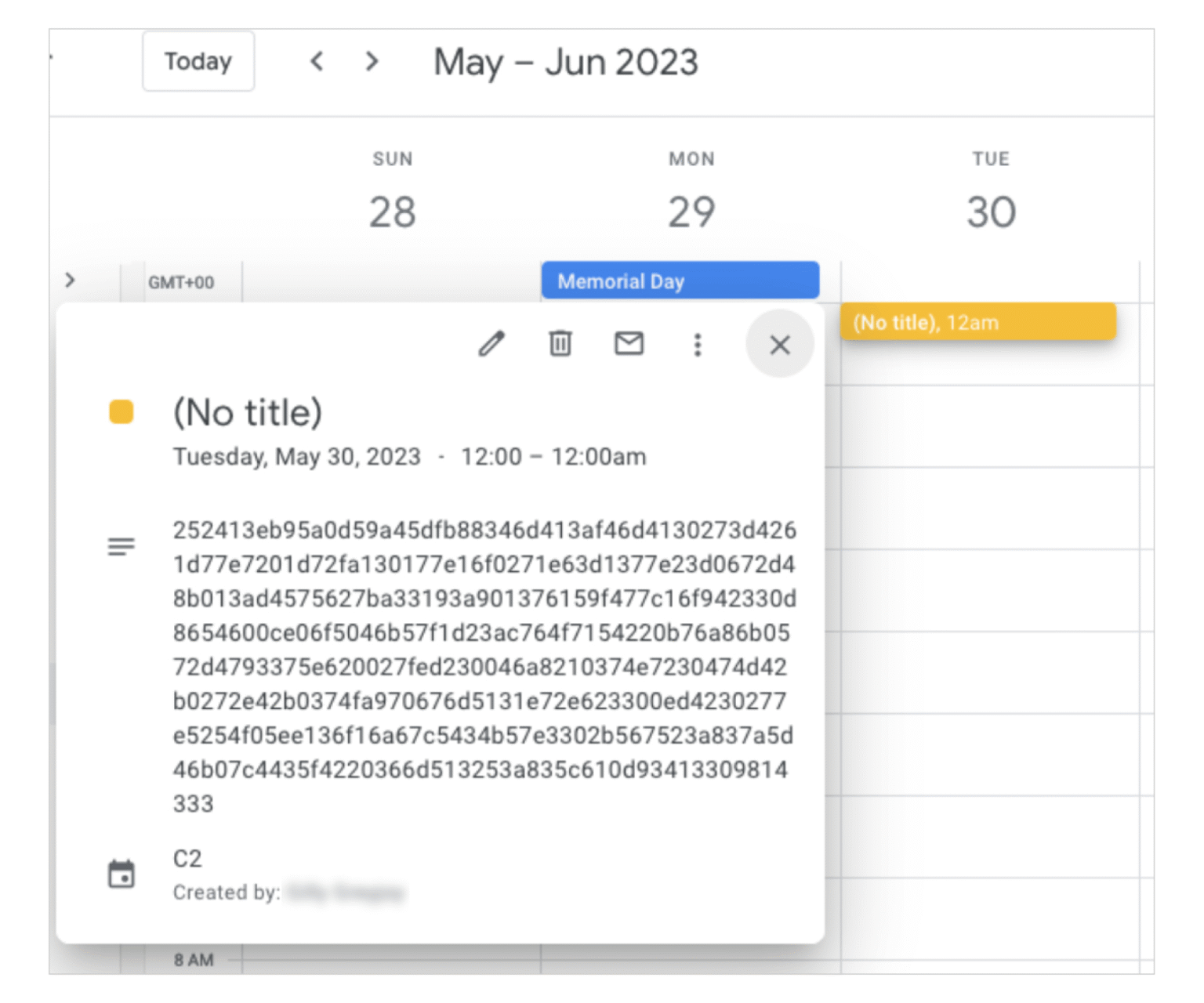
TOUGHPROGRESS uses Google Calendar as a stealthy command-and-control (C2) channel. It creates hidden events on specific hardcoded dates to exfiltrate stolen data and receive commands. The malware encrypts both data and commands using XOR keys and compresses messages with LZNT1. Commands are placed in Calendar event descriptions, retrieved and decrypted by the malware, then executed on the infected system. Results are encrypted and uploaded back as new calendar events, effectively turning Calendar into a covert communication tool.


“To disrupt APT41 and TOUGHPROGRESS malware, we have developed custom fingerprints to identify and take down attacker-controlled Calendars.” continues the report. “We have also terminated attacker-controlled Workspace projects, effectively dismantling the infrastructure that APT41 relied on for this campaign. Additionally, we updated file detections and added malicious domains and URLs to the Google Safe Browsing blocklist. “
Google GTIG and Mandiant Consulting alerted affected organizations, sharing TOUGHPROGRESS network logs and threat intel to support detection and response efforts.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, APT41)