Akira ransomware gang used an unsecured webcam to bypass EDR

The Akira ransomware gang exploited an unsecured webcam to bypass EDR and launch encryption attacks on a victim’s network.
Cybersecurity researchers at S-RM team discovered a novel attack technique used by the Akira ransomware gang. The ransomware group used an unsecured webcam to encrypt systems within a target’s network, bypassing Endpoint Detection and Response (EDR).
The researchers observed that the Akira ransomware was initially blocked by the EDR installed on the victim’s systems, which identified and quarantined the ransomware binary, preventing its deployment across the victim’s network.
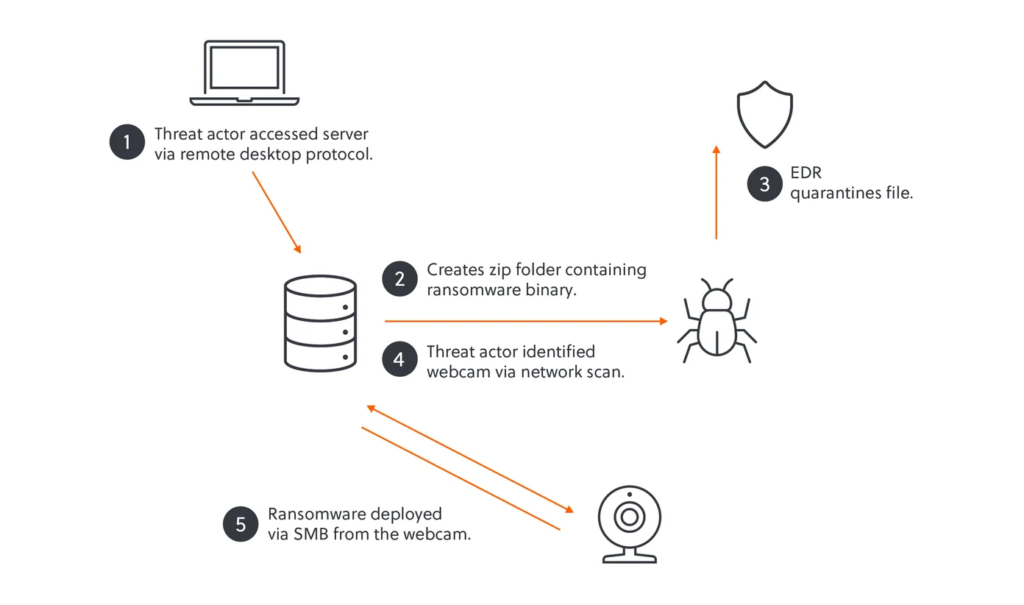
The Akira ransomware group gained access to the network via a remote access tool, using AnyDesk for persistence and exfiltrating data. The attacker then moved via RDP to a server and attempted to deploy ransomware as a password-protected zip file, but the victim’s EDR tool blocked it. Realizing EDR was active, they pivoted by scanning the network for vulnerable devices. They found unsecured IoT devices, including webcams and a fingerprint scanner, using them to bypass security defenses and successfully deploy the ransomware.
The attacker exploited a webcam affected by critical vulnerabilities, including remote shell access and no EDR protection. The IoT device was running a lightweight Linux OS, that was the perfect target for Akira’s Linux ransomware variant. The lack of monitoring allowed the attacker to deploy ransomware, unnoticed by the victim’s security team, who failed to detect suspicious SMB traffic. Akira successfully encrypted files across the network.
“After identifying the webcam as a suitable target, the threat actor began deploying their Linux-based ransomware with little delay. As the device was not being monitored, the victim organisation’s security team were unaware of the increase in malicious Server Message Block (SMB) traffic from the webcam to the impacted server, which otherwise may have alerted them.[1] Akira was subsequently able to encrypt files across the victim’s network.” reads the report published by the S-RM team.

The Akira ransomware attack reveals the risks of overlooked IoT devices, evolving cyber threats, and EDR limitations. Weak links like unpatched IoT devices can be exploited, as seen with Akira’s shift from Rust to C++ for broader attacks. Despite EDR’s importance, gaps in coverage or misconfigurations allow attackers to bypass defenses, emphasizing the need for comprehensive security strategies.
“Preventing and remediating novel attacks like this one can be challenging. At a minimum, organisations should monitor network traffic from their IoT devices and detect anomalies.” concludes the report. “They should also consider adopting the following security practices:
Turn devices off: Keep IoT devices switched off when they are not in use.”
- Network restriction or segmentation: Place IoT devices on a segmented network that cannot be accessed from servers or user workstations or restrict the devices’ communication with specific ports and IP addresses.
- Internal network audit: Regularly audit devices connected to the internal network, which may help to identify security weaknesses or rogue devices implemented by a threat actor.
- Patch and device management: Keep devices, including IoT devices, regularly patched with the most recent update. Ensure default passwords of IoT devices are changed to unique and complex ones.”
The Akira ransomware has been active since March 2023, the threat actors behind the malware claim to have already hacked multiple organizations in multiple industries, including education, finance, and real estate. Like other ransomware gangs, the group has developed a Linux encryptor to target VMware ESXi servers.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Akira ransomware)